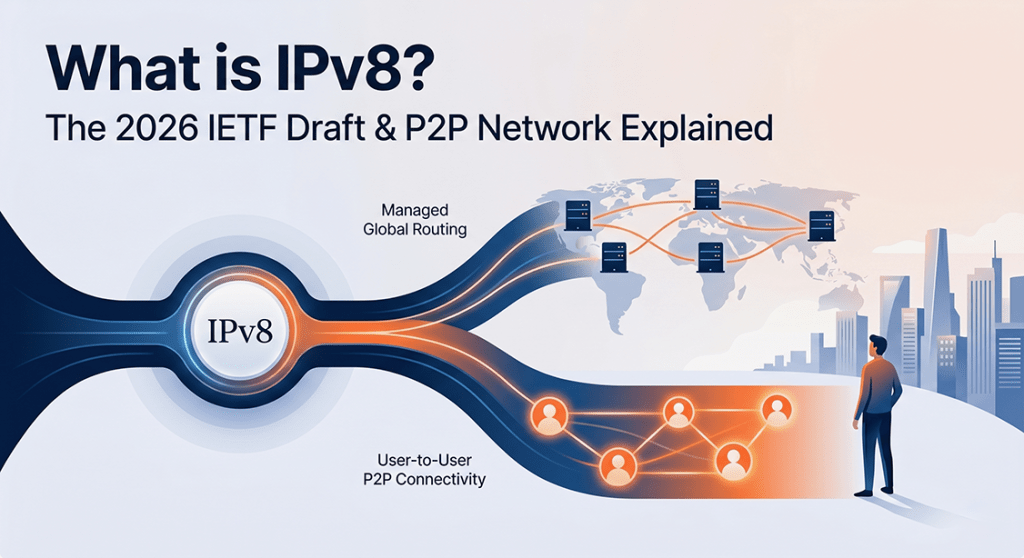
TL;DR: The term “IPv8” currently refers to two completely distinct technologies. In hardware and routing, it is a controversial April 2026 IETF Internet-Draft proposing a 64-bit architecture to solve IPv4 exhaustion without the migration headaches of IPv6. In software engineering, it is a heavily researched, open-source Python library by TU Delft used to build highly secure, decentralized, peer-to-peer (P2P) networks that bypass traditional centralized internet infrastructure entirely.
If you work anywhere near network architecture, you already know the painful reality of our current infrastructure. For over two decades, the industry has been fed a singular narrative: IPv4 exhaustion is complete, we are entirely out of addresses, and the only way forward is the agonizing, expensive migration to IPv6.
Yet, here we are in 2026, and the majority of the world is still duct-taping legacy networks together using Carrier-Grade NAT (CGNAT) and endlessly complex subnets. Why? Because ripping out existing infrastructure to run a dual-stack IPv6 transition is an operational nightmare. Network engineers want the infinite space of IPv6, but they desperately crave the simplicity of IPv4.
Recently, a massive rumor has been tearing through Hacker News, Reddit, and engineering Slack channels. The buzzword is IPv8.
Is it a typo? A late April Fools’ joke? A conspiracy?
Actually, it’s none of the above. If you look closely at what’s happening in computer science right now, “IPv8” isn’t just one thing. The term currently describes two completely different, cutting-edge technologies. One is a highly controversial proposal trying to rewrite the rules of global internet routing. The other is an underground, battle-tested software library designed to bypass standard internet checkpoints entirely.
Let’s cut through the noise, drop the robotic tech-jargon, and look at what IPv8 actually is.
The Network Engineer’s Dream: The April 2026 IETF Draft
Let’s start with the development that has hardware vendors talking.
In April 2026, an Internet-Draft officially titled draft-thain-ipv8 was submitted to the Internet Engineering Task Force (IETF), the governing body of internet architecture.
This new IPv8 draft basically asks a forbidden question: What if we stopped trying to force an IPv6 migration and just built a protocol that actually makes sense for the people running the servers?
IPv4 failed because its 32-bit address space wasn’t big enough for a planet full of smart devices. IPv6 tried to fix this with a massive 128-bit space, but doing so created a completely different language that legacy hardware simply couldn’t read.
The IPv8 draft proposes a brilliant middle ground: a 64-bit architecture. Know more about IPv8 Kills VPNs.
How the Math Actually Works
Instead of the terrifying, unreadable hexadecimal strings of IPv6, the IPv8 draft keeps the familiar dotted-decimal format you already know, but doubles it into an r.r.r.r.n.n.n.n format.
- The first half (
r.r.r.r) is the routing prefix. It mathematically locks to an ISP or enterprise’s Autonomous System Number (ASN). - The second half (
n.n.n.n) acts exactly like a standard IPv4 host address.
This simple structural change instantly grants every single network provider on earth a pool of 4.2 billion IPs, killing the need for NAT entirely. Furthermore, because the routing is tied directly to the ASN, it theoretically solves BGP routing table bloat, collapsing the bloated global routing table down to essentially one entry per network.
But the real reason this draft is going viral is its backward compatibility. IPv4 is natively baked into IPv8. If a packet has a routing prefix of all zeros, the hardware just treats it like a legacy IPv4 address. You wouldn’t need to rip and replace your internal network overnight.
The Reality Check
So, are ISPs rolling out IPv8 tomorrow? Not a chance.
While the draft is beautiful on paper, it proposes shifting security directly into the IP layer, demanding that every packet be authorized by an OAuth2 token. Validating a cryptographic token on every single packet at core routing speeds (like 400 Gbps) is currently physically impossible for modern silicon. Right now, this draft is an incredible thought experiment—but it highlights exactly how frustrated the industry is with our current options.
The Underground Web: TU Delft’s P2P Library
Now, if you pivot away from hardware routing and look at software engineering, you’ll find that “IPv8” already exists. It’s real, it’s heavily documented in academic journals, and developers are actively using it.
In the software world, IPv8 is an open-source Python library—maintained on GitHub as py-ipv8—built by researchers at the Delft University of Technology (TU Delft) in the Netherlands. They’ve been quietly perfecting it for nearly two decades.
This version of IPv8 doesn’t care about your router or your ISP. It is an overlay for decentralized P2P networks designed to make central servers—and the tech giants that own them—irrelevant.
Identity Over Infrastructure
When you use the regular internet, your IP address dictates who and where you are. In the TU Delft IPv8 ecosystem, physical IP addresses are completely ignored.
Instead, peers connect to each other using cryptographic public keys. You aren’t connecting to a server farm in Virginia; you are connecting to a mathematically verified human identity. This makes IP spoofing and middle-man attacks practically impossible.
Even better, the library is famous for its aggressive UDP hole-punching. It tunnels through strict corporate firewalls, allowing two locked-down computers to talk directly to each other without needing a centralized relay server to introduce them.
The Academic Validation
This isn’t just a hobby project. This IPv8 library is the foundation for a massively scalable distributed ledger that does what blockchain does, but without the environmental disaster of cryptocurrency mining.
If you want to read the peer-reviewed science behind it, the foundational paper is TrustChain: A Sybil-resistant scalable blockchain (Otte et al.). Published in Future Generation Computer Systems, this paper demonstrates how the IPv8 framework effectively prevents “Sybil attacks” (fake identity clustering) while processing transactions faster than legacy networks like Bitcoin.
Developers are using this IPv8 framework to build Self-Sovereign Identity (SSI) systems. Imagine a digital passport that you own completely on your mobile device, which can’t be revoked by a government or tracked by a corporation. That is the kind of internet the IPv8 software library is currently building.
The Bottom Line
When someone asks you about IPv8, you now have the upper hand.
Are they talking about the brand-new April 2026 IETF draft? If so, they are talking about a radical routing proposal that aims to fix the massive mistakes of IPv6 by wrapping legacy IPv4 in a highly efficient 64-bit blanket.
Or are they talking about the TU Delft Python library? If so, they are talking about a battle-tested software framework that allows developers to build secure, serverless applications that completely bypass traditional internet checkpoints.
Either way, IPv8 proves one thing: the internet isn’t finished. We aren’t permanently stuck with the clunky, aging infrastructure we have today, and the smartest minds in the world are actively building the escape routes.
Leave a reply to IPv8 Kills VPNs: Layer 3 Zero Trust & Crypto Mesh Explained – safa.tech.blog Cancel reply